Duration 3:35
How to hack: SQL INJECTION UNION ATTACK, DETERMINING THE NUMBER OF COLUMNS RETURNED BY THE QUERY
Published 19 Feb 2022
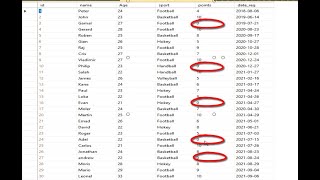
#burpsuite #hacking #hacker How to Solve: SQL INJECTION UNION ATTACK, DETERMINING THE NUMBER OF COLUMNS RETURNED BY THE QUERY Hit Like and Subscribe! Thank you! Hit: Access the Lab After the home page on your screen: copy paste the url for the Target Scope Set the browser network setting to manual proxy (127.0.0.1:8080) Burp Proxy | Intercept-tab | Turn off the intercept| Click: Intercept is on - button | Intercept is off Burp Proxy: HTTP History (refresh the Fox browser) Click: Pets - tab Go to Proxy - tab | HTTP history | Check GET - method column | /filter?category=Pets at the URL-column | Send it to Burp Repeater (Ctrl-R) Go to Repeater - tab | Request -side 1st try | Modify Row 1: GET /filter?category=Pets'+UNION+SELECT+NULL-- HTTP/1.1 Click Send - Request button | Response-side | Row 1 | 500 Internal Server Error 2nd try | Modify Row 1: GET /filter?category=Pets'+UNION+SELECT+NULL,NULL-- HTTP/1.1 Click Send - Request button | Response-side | Row 1 | 500 Internal Server Error 3rd try | Modify Row 1: GET /filter?category=Pets'+UNION+SELECT+NULL,NULL,NULL-- HTTP/1.1 Click Send - Request button | Response-side | Row 1 | 200 OK We got the 3 columns returned by the query. Lab: Solved Thank you for watching!
Category
Show more
Comments - 0






























![فهد العرادي سناب [ 363 ] مفاجأة دكتورة خلود في العيادة بعد ما سوت العملية](https://i.ytimg.com/vi/mUQjkkO3NKU/mqdefault.jpg)

